As the cyber world gradually converges with the physical one and “Digital Transformation” becomes the emerging phrase that encompasses all efforts to improve productivity and minimize costs, the impact of cyberattacks is no longer limited to data breach and financial consequences. The attacks can have catastrophic repercussions on the physical world and may even result in a loss of human lives, just like it regretfully happened recently at a German hospital.
Industrial control systems (ICS) range from very small systems (elevator, power, HVAC, refrigeration, water heater systems) to very large industrial systems (refineries, chemical and pharmaceutical manufacturing, power plants). While these systems were traditionally independent, Digital Transformation has increased the connectivity between them. Digital Transformation has also connected many of them with corporate and vendor systems in datacenters and the cloud, further complicating and growing the cyber risk profile of the organization.
What seems to remain largely unnoticed is the pivoting risk the hyperconnectivity of systems has on health, safety and environment (HSE). It takes one insecure system in the entire value chain to take down an entire manufacturing operation that results in HSE consequences.
This article reviews the links between ICS and HSE. It also presents an ICS cybersecurity approach towardssafeguarding HSE in an efficient, collaborative, comprehensive and cost-effective manner.
What is Health, Safety, and Environment (HSE)?
Health, Safety and Environment (HSE) is a framework of actions that organizations must take to ensure the protection of the environment without harming the health and safety of their employees or local communities.
• The safety factor of the framework involves the establishment and enforcement of processes and procedures to identify hazardous conditions and their consequences and implement adequate countermeasures to reduce the possibility of safety accidents.
• The health of employees, customers, patients, or local communities is safeguarded by the development of high-quality processes and policies to reduce the possibility of causing harm to people.
• The environmental factor concerns the enforcement of practices, policies and procedures compliant to regulations to safeguard the environment, such as reducing the carbon footprint or minimizing emissions and waste.
Organizations based in the United States are subject to HSE regulations in the Code of Federal Regulations, particularly CFR 29, 40, and 49. In addition, the Occupational Safety and Health Administration (OSHA) has numerous regulations as well as incident reporting requirements, audits, and fines to enforce best practices and ensure the health and safety of employees and the environment.
How ICS benefits and endangers HSE?
Nowadays, as part of the industries digitalization efforts, industrial control systems (ICS) are being embedded into various levels of business processes, from field devices, such as smart meters or relays, to highly critical computing systems. These systems remotely monitor and control operational sites, gathering data from sensors, monitoring the local environment, and transmitting data to enable decision-making.
The use of ICS greatly enhances efficiency since they can centrally control and monitor the various production phases and identify faults and hazards through data acquisition and auditing. By providing early warning notifications for hazardous conditions, ICS systems not only reduce their impact and augment efficiency, but they also benefit the health and safety of employees and preserve the environment, because safety teams can take action to remedy these conditions.
However, no system is immune to vulnerabilities. Besides the benefits ICS systems introduce, they create novel cybersecurity risks and challenges and expand the threat landscape. In industrial settings, because of criminal activity targeting these systems, cybersecurity incidents can result in financial losses, equipment damage, environmental consequences and even injury or loss of life.
These cybersecurity incidents and breaches happen when organizations are negligent and fail to establish and enforce strong security controls to protect against emerging threats. While in some sectors the damage is typically financial, in industrial sectors the damage can be physically devastating as well. For example, when the air or the water is polluted because of a cyber-attack, or when people’s health and safety is jeopardized, the consequences are far-reaching. A recent cyber incident in Florida is just a simple example of what can go wrong.
As cyber-attacks on the industrial cyber-physical systems increase, the risk of physical consequences exponentially increases. Sophisticated cyber-attacks on cyber-physical systems a likely to result in multiple fatalities and significant financial, regulatory and reputational loss. An article published by Gartner estimates the financial impact to be close to $50 billion by 2023. The article goes further in suggesting 75% of the CEOs being personally liable for such incidents.
ICS cybersecurity is a shared responsibility
To mitigate these threats to cyber-physical systems and limit their consequences, the industry is developing stricter regulations. For example, the North American Electric Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) standards continue to be enhanced to regulate and enforce cyber and physical security controls for the U.S. bulk power grid.
Considering the far-reaching effects of cyber-physical incidents and attacks, industry leaders must realize that cyber risks are as possible and impactful as the “traditional” safety risk they are used to confront. In fact, cyber threats can be the source of safety risks if appropriate measures to prevent them are lacking.
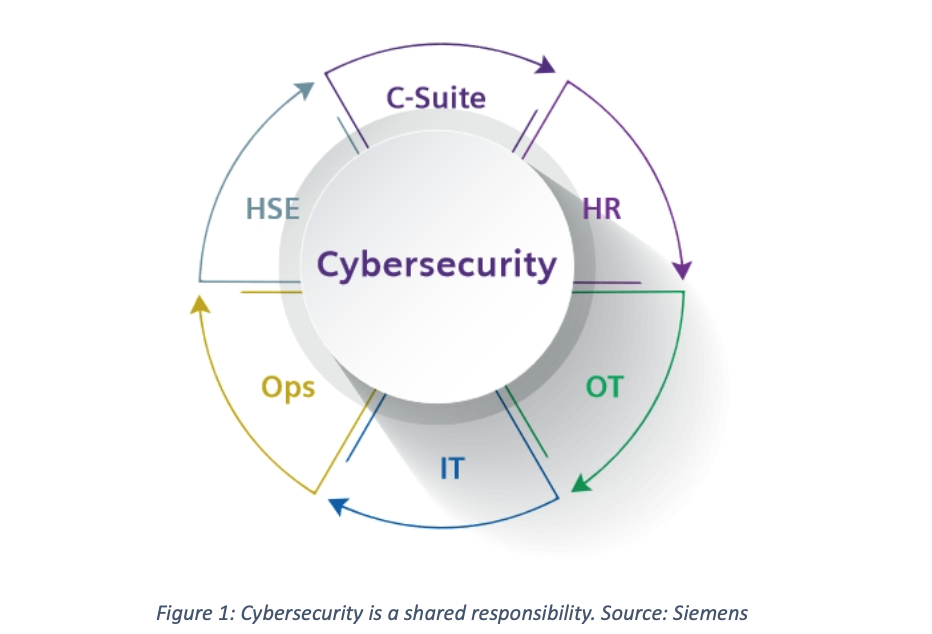
It is also important to understand that cyber risk is not “IT’s job.” Long since are the days when IT and OT worlds were siloed. Technology has blurred the boundaries between IT and OT. An isolated approach to cybersecurity creates more blind spots that can be exploited by cybercriminals. Siemens mentions in a report:
Cybersecurity should be a shared responsibility of all employees in a company, from the executive suite to close collaboration among OT, operations, and enterprise IT. Cybersecurity should also engage health, safety, and environmental (HSE) teams, because of the potential HSE impacts of a severe security breach. HR must be involved, too, because all employees need to be aware, trained, and accountable for their potential roles, intentional or not, in opening the doors — physically or virtually — to attackers.
(Three Ways Oil and Gas, 4)
How can ICS cybersecurity safeguard HSE processes?
Organizations can strengthen the ICS cybersecurity posture and safeguard HSE processes by taking an approach similar to protecting the safety and reliability of safety systems. Strong and robust cybersecurity policies and practices can help detect and prevent imminent attacks targeting ICS systems and minimize the consequences of possible incidents.
Industries should follow a risk-based approach, just like the one they already know from the process safety lifecycle. Effective ICS cybersecurity is a risk-based process and involves four repeating steps:
Identify and Assess risk.
Identifying cyber risks and hazards can be done by leveraging the well-established Hazard and Operability (HAZOP) studies and by giving the processes a cyber twist. A cyberHAZOP builds on the HAZOP study and enables deeper level collaboration of experts and professionals across diverse domains – plant engineering & operations, HSE, OT and IT – to gain interdisciplinary insight and knowledge of all processes affected by ICS cybersecurity.
Another instrument used by process safety specialists to evaluate risk, such as Level of Protection Analysis (LOPA) can be adapted to further assess the mitigation requirements for ICS cybersecurity.
LOPA is an “event driven” approach utilized by professional engineers to identify the essential barriers(“Protection Layers”) for reducing the operational risks and to then determine the monitoring indicators for each barrier. A cyberLOPA builds on this concept of independent protection layers for assessing the resistance of physical and cyber-physical systems to cyber attacks. Organizations’ cybersecurity postures stand to benefit from a combined investigation and assessment of the weaknesses in cyber, cyber-physical, and physical systems to then apply the appropriate cost-effective and reliable protective measures. Sometimes physical or mechanical controls can be sufficient to avert a cyber incident and therefore does not require complex and expensive cybersecurity solutions.

Manage risk.
The increasing use of IT capabilities in industrial environments and the resulting complexity in industrial settings, increases the risk of failures and their consequences. Therefore, it’s necessary that all risks are continuously identified, assessed, and mitigated as part of a cyber operations & maintenance system. Applyingindustry-specific cybersecurity standards, such as NERC CIP, ISA/IEC 62443, CFATS, NIST Cybersecurity Framework, and collaborating across other domain standards such as ITIL (for IT), IEC 61508 and ISA/IEC61511 (for functional safety) can help increase cyber resilience capabilities.
Enhance posture.
As part of the overall cyber operational resilience management (cyberORM), updates to the established ICS cybersecurity operations & maintenance processes should include audits, assessments, drills, personnel competency training, and access to intelligence provided by vendors, CCCS, CISA or other federal agencies. Reviewing standing processes and evolving them to adapt to the changing threat environment is a crucial part of ICS cybersecurity resilience. It exposes new blind spots and gaps due to the identification of novel vulnerabilities in existing technologies and the continuous introduction of new technologies.
How ORIGNIX helps
Boards need to continuously assess their effectiveness in addressing cybersecurity, both in terms of their own fiduciary responsibility as well as their oversight of management’s activities. Our cyber Process Risk Analysis (cyberPRA) and cyber Operations Resilience Management (cyberORM) services work together and are customized to fit the needs of our critical infrastructure clients.
ORIGNIX delivers bespoke cybersecurity engineering services for inherently safer design and operation of industrial processes. We utilize systematic cyber and operational risk assessment using well-established techniques and templates. Our cyberPRA methodology identifies potential gaps, hazards, vulnerabilities, and independent protection layers associated with engineered industrial processes at plant facilities. Our cyber Hazard and Operability (cyberHAZOP) study is a component within cyberPRA that helps clients systematically identify and qualify the risks on their cyber-physical systems’ (CPS) availability and reliability. Our cyberORM system framework can help you fast-track and achieve the desired functional and strategic risk tolerance level of your CPS. Our methods are based on recognized and generally accepted good engineering practices (RAGAGEP), including internationally recognized industry standards ISO 27001/2, ISA/IEC 62443, ISA/IEC 61511, and NIST 800-82.
For more information, click here.



