Digital attackers are increasingly targeting Operational Technology (OT) assets used by electric utilities and other organizations. In its Threat Intelligence Index 2020, for instance, IBM X-Force found that the number of events targeting OT and Industrial Control Systems (ICS) increased by over 2000% between 2018 and 2019. The volume of OT attacks in 2019 was so high that it exceeded the combined number of attacks recorded for the previous three years.
OT’s ongoing convergence with Information Technology (IT) could be contributing to this rise in attacks. As noted elsewhere on this website, many organizations are pairing their OT assets with sensors, actuators and other web-connected Industrial Internet of Things (IIoT) devices in an attempt to optimize their industrial processes and minimize downtime. The downside here is that many of those OT assets were not designed with today’s IT security risks in mind. Some are legacy systems that are decades old and that have their own proprietary protocols—equipment that’s ill-prepared against brute force login attempts, ransomware attacks and other common IT security threats. Not only that, but many constituent systems are interdependent with one another. This means that IT security threats present a systemic risk in that attackers could leverage one OT or ICS compromise to affect other industrial systems and devices.
These findings raise an important question: where is OT cyber security going for electric grid organizations? How are the industry’s OT security priorities moving forward in an effort to address these digital risks?
A Glimpse into the Sector’s Priorities
The Electric Power Research Institute (EPRI) sought to answer this question in a report entitled “Cyber Security for the Electric Grid: R&D Progress and Emerging Priorities.” Specifically, the nonprofit organization spoke with numerous CIOs, CISOs and other utility executives who were responsible for their electric organization’s cyber security. Those interviews uncovered five priorities for utility organizations’ OT security efforts going forward.
Priority #1: Automating Cyber Security Capabilities
EPRI noted in its paper that the electric grid is undergoing a digital transformation:
Grid modernization efforts to improve the reliability and flexibility of the grid result in the deployment of digital equipment on all aspects of the grid – Generation, Transmission, Distribution, and Distributed Energy Resources (DER) at customer locations. This means more data and detection of potential cyber security events occurring faster than humans can respond.
Those executives whom EPRI interviewed were well aware of this fact. When asked by EPRI to name their highest OT security priority for the coming year, close to a quarter (23%) named threat and vulnerability management first. This was followed by event & incident response as well as asset, change & configuration management at both 17%.
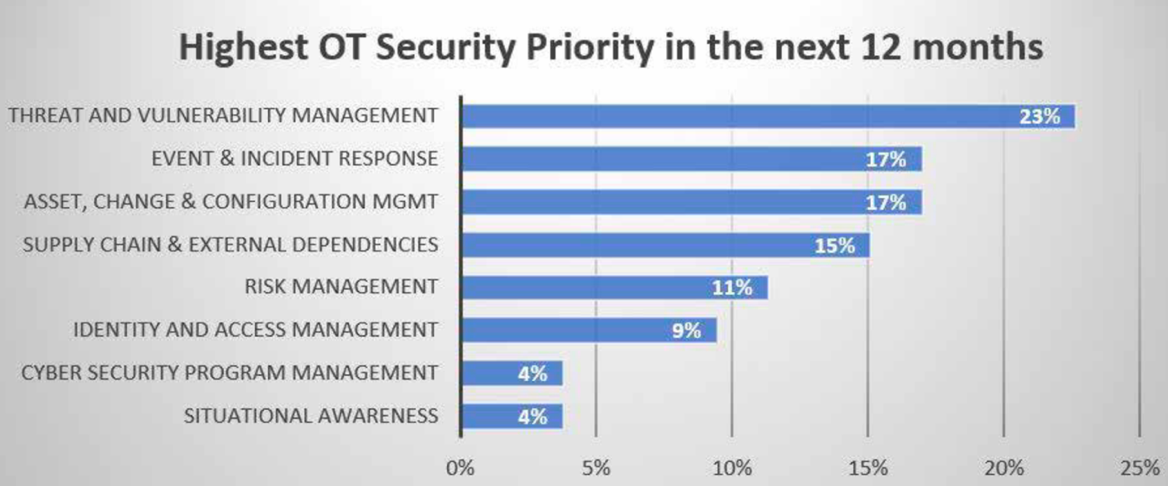
Examining these insights, EPRI found that executives were most interested in advancing automation across those three categories. Automation can help pick up on security incidents that human analysts might have missed. Not only that, but it can also increase the speed and accuracy of analysts themselves, thereby empowering them to detect potential security issues faster and not waste their time on needlessly manual tasks like combing through system alerts.
Priority #2: Supply Chain Risks for Procurement and Installed Equipment
EPRI explained that several stakeholders are working to advance supplier cyber security practices for electric grid organizations. The nonprofit organization named the North American Transmission Forum (NATF), whose Supplier Cyber Security Assessment Model helps give organizations a consistent way of conducting a risk assessment for potential and existing suppliers. It also noted that the Edison Electric Institute (EEDI) and the North American Electric Reliability Corporation (NERC) are spearheading efforts to tackle this problem.
Priority #3: Quantifiable Data to Support Risk Model and Decision-Making
One of the biggest gaps confronting utility organizations’ OT security efforts is the lack of data-driven OT security metrics, EPRI explained in its report. To address this problem, EPRI released its OT Security Metrics Tools. These resources help companies to calculate their OT security posture using 56 metrics based on 96 different data points pertaining to their industrial operations. More than 30 utilities helped EPRI to improve these metrics leading up to its report.
Priority #4: Cloud Security for Real-Time Systems – Potential Opportunities
In its conversations with the electric executives, EPRI found that the “cloud” and its integration into future real-time applications was the topic that came up the most. EPRI identified a shift in the way executives discussed this matter, with many of its respondents asking about the security risks of using the cloud and the security architectures that were needed to help them safely leverage the cloud. Some also revealed that they had begun to implement organizational changes to support this shift to the cloud.
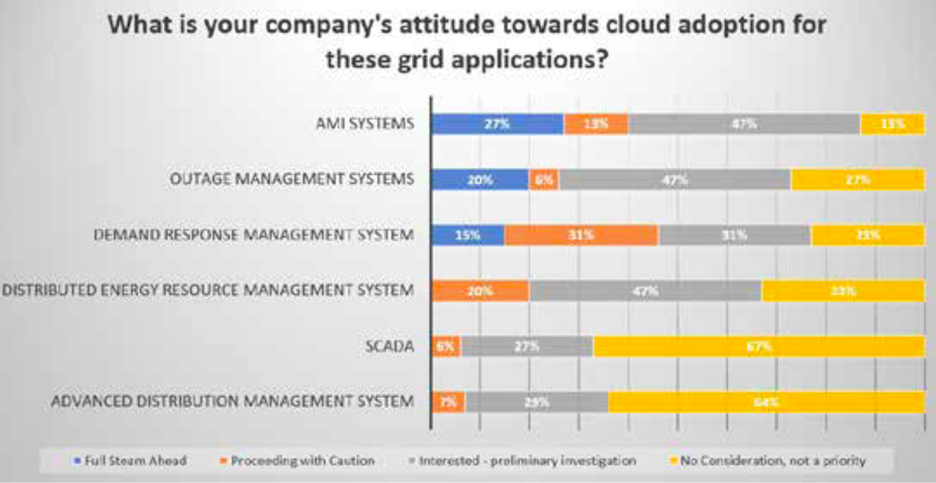
Executives were particularly interested in adopting the cloud to serve their Advanced Metering Infrastructure (AMI) systems, outage management systems and demand response management systems. They were less enthusiastic about using the cloud for their Distributed Energy Response (DER) management systems, supervisory control and data acquisition (SCADA) assets as well as their advance distribution management systems, as relayed in the graph presented below.
After it had discussed these issues with the utility executives, EPRI launched a new collaborative research project called, “Cloud Security Reference Architecture for Real-Time Utility-Based Applications.” This project will seek to accomplish five tasks: perform a risk analysis of a utility cloud application determined by each utility, identify security controls and tools guidance, identify approaches to demonstrate compliance and security best practices, produce a security reference architecture for the specific utility application and share non-proprietary results from ALL the cloud applications evaluated.
Priority #5: Cyber Security for DER
Finally, EPRI said that it will be working with utilities and stakeholders to evaluate DER technologies in its research lab. Part of that process will involve exploring cyber security practices for DER devices. Additionally, EPRI said that it will continue to hold its annual DER/Grid-edge Cyber Security Workshop to help promote DER cyber security.
Security in the Meantime
Organizations need to continue protecting their OT assets while the priorities identified by EPRI move forward. To do this, they can work with a trusted managed services provider like ORIGNIX. The firm’s cyberPRA methodology helps to identify and prioritize security risks that affect its customers’ industrial processes. Next, its cyberORM methodology helps organizations track their industrial cybersecurity requirements, update their industrial cybersecurity policies and manage their corresponding assets. Click here to learn more about ORIGNIX can help.